Ups and Downs in Academia
We all know it – Academia is a…
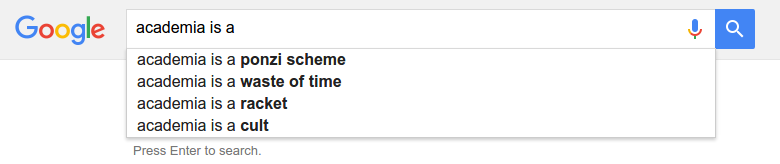
OK, I’ve expected to see something else here.
Still, it’s really interesting to see how good and bad experiences following so tightly. I guess, I should start with the bad one to end on a high note and to be in a better mood after writing this post.
<Rant>
Already in March, Google Scholar pointed me to a technical report that was citing my GNU Radio WiFi transceiver. The context was not really gently:
Very recently several attempts were made to develop an IEEE802.11abg compatible stack that reaches 54Mbps [6], [5], [7]. However, this open source GNU Radio based implementation is limited to QPSK and not able to correctly receive neither 16-QAM nor 64-QAM modulated signals and the reported evaluation only considers packets below 100 Bytes [6].
I dropped them an email, mentioning that I’m the author of said attempts, asking for what was going wrong. As it turned out, they used an N210, configured 20MHz, and oh wonder, there was an uncompensated CIC filter. (Yes, the filter that UHD informs you about each and every time you start the flow graph.) Long story short, they acknowledged that their claim was wrong and updated their technical report.
Five months fast forward – Google Scholar again. The authors published a paper. Looking at the conference website, it becomes clear that about the same time, they submitted a paper to ACM WiSec 2016, which claims:
While there is an existing implementation of Wi-Fi receiver [2] on GNU Radio, it is not functional for rates beyond 18 Mbps.
So this means that even though they knew about their mistake and that this claim did not hold, they still put it in the paper to make their work more relevant. I mean it’s one thing if somebody misunderstands a paper, but on purpose? Seriously?
To backup their claim and to confuse the reviewer, the authors cite a demo paper, which they knew from the emails was out of date. But still it did not help. While the channel estimation algorithms were not as good as now, this demo already showed that it does support all modulation and coding schemes. Sorry, but this is very – let’s say – questionable practice.
If you already think that that’s a shame, then keep on reading.
While they were at it, they seemingly also came to know our Scrambler Attack, a novel attack on the privacy of WiFi networks, which was, meanwhile, picked up and continued by quite some other researchers.
In the same WiSec paper, the authors continue:
Recent work [30] discovered that for some chipset manufacturers, scrambling seeds are generated in a free-wheeling mode with some specific shift distances which are used to distinguish the device models.
This is exactly what we wrote in our paper. Now guess what’s behind [30] – exactly, a paper that builds on ours, obviously chosen to avoid citing our paper that actually discovered it.
Really, I don’t know what to say about that, since this is just wrong on so many levels. For me, it’s really disappointing to see how people behave in this scientific community.
</Rant>
Fortunately, there is also a short story from the bright side of life. Again, Google Scholar pointed me to a paper that will be presented at ACM SIGCOMM 2016.
To put it in context, SIGCOMM is the conference on all kinds of data communications. If I had an idea, ten-times better than everything before, I still would not even consider submitting to SIGCOMM.
I’m, therefore, extremely happy to see that researchers from the University of Washington use our WiFi transceiver and exploit our findings regarding the scrambler seeds to do awesome work in the context of energy-efficient, backscattered communications.
So, not all hope is lost… let’s see what the future brings :-)
